The Cyber Risk Assessment Your Business Needs
ACSIA CRA analyzes your organization’s security level, identifies potential vulnerabilities and calculates your cybersecurity rating, so you will have a clear understanding of your cyber risk.
Your ACSIA Cyber Security Assessment Is On Its Way!
A Win For Audit And Compliance
ACSIA CRA performs a comprehensive analysis of a company’s cyber posture, focusing on the exposure of its services and information that may be vulnerable to cyber attacks.
Your ACSIA Cyber Security Assessment Is On Its Way!
A Win For Audit And Compliance
ACSIA CRA performs a comprehensive analysis of a company’s cyber posture, focusing on the exposure of its services and information that may be vulnerable to cyber attacks.
Quickly Identifies External Risks
Quickly Identifies External Risks
ACSIA CRA promptly checks the cybersecurity posture of your company, documenting your external attack surface, highlighting how your business may be at risk.
Deep Visibility Of Your Attack Surface
ACSIA CRA uses multiple sources to scan your public attack surface. ACSIA CRA’s analysis is not limited to the external perimeter but also includes digital identities.
Constantly Updated
If new vulnerabilities are discovered, ACSIA CRA’s index automatically updates allowing your team to actively monitor your perimeter.
Easy To Use
ACSIA CRA only needs simple and easy to find information or inputs to identify your company (VAT and web domains).
Facilitates Improvement
ACSIA CRA identifies mis-configurations, helping your team to improve security policies about account and device usage.
Clear Information
ACSIA CRA’s dashboard is easy to understand with informative dashboards and reports suitable for non technical stakeholders.
ACSIA CRA At Work
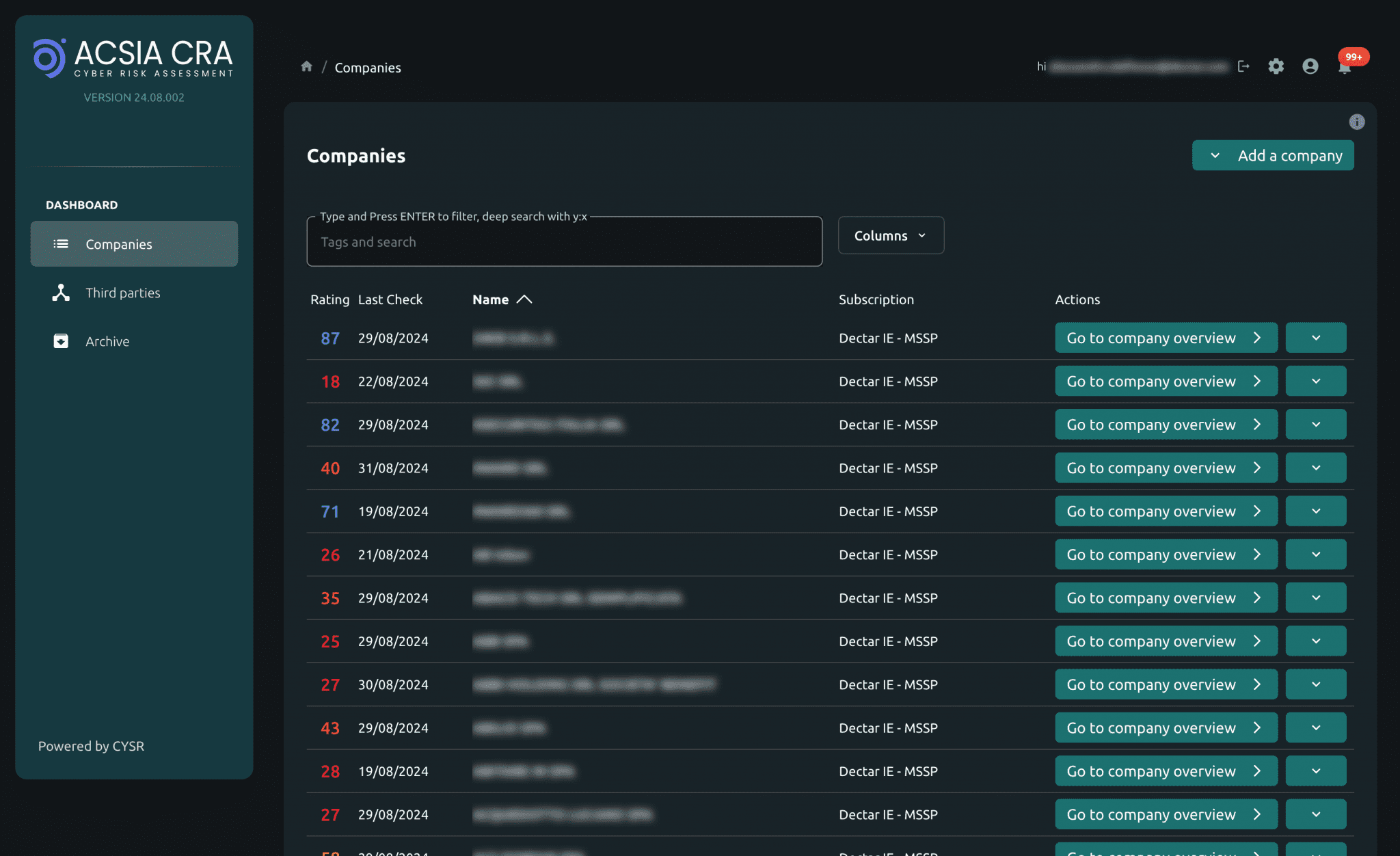
Check Your Business Exposure
ACSIA CRA assesses the IT security of your public facing assets, analyzing risks and documenting the status of your business cyber security.

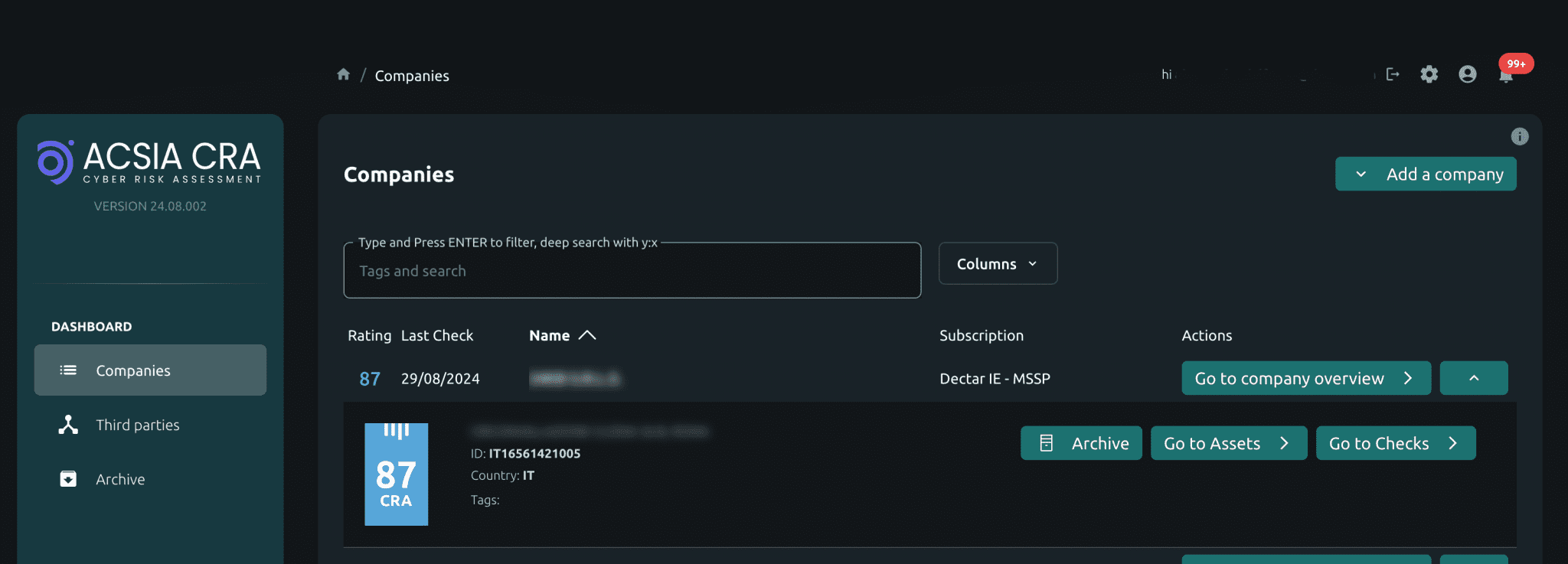
Discover And Map Your Security Posture
ACSIA CRA conducts passive scans to map and enumerate vulnerabilities. Our risk assessment provides your business with a clear picture of where issues, exposure or security weaknesses may lie.
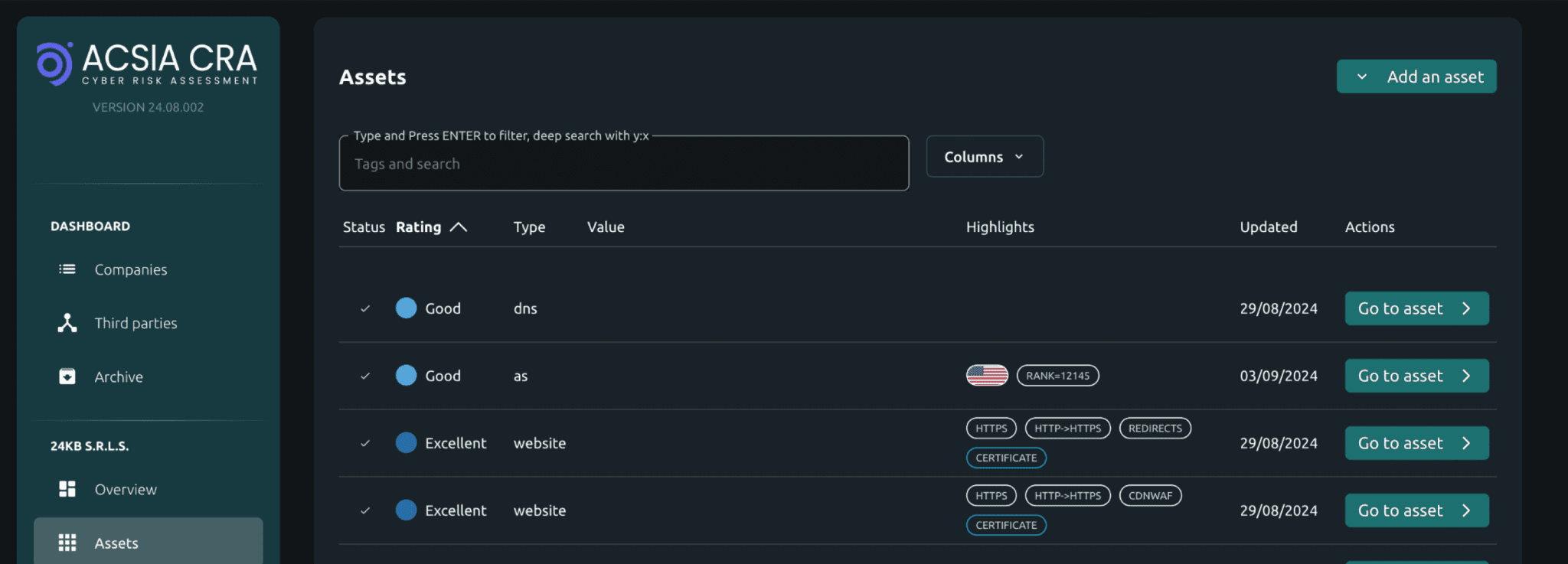
Scan Thousands Of Assets
You can quickly detect any potential exposure of your company’s assets. ACSIA CRA scans your public attack surface performing thousands of tests. It behaves similarly to malicious software in the analysis phase of cyber attacks on the target.

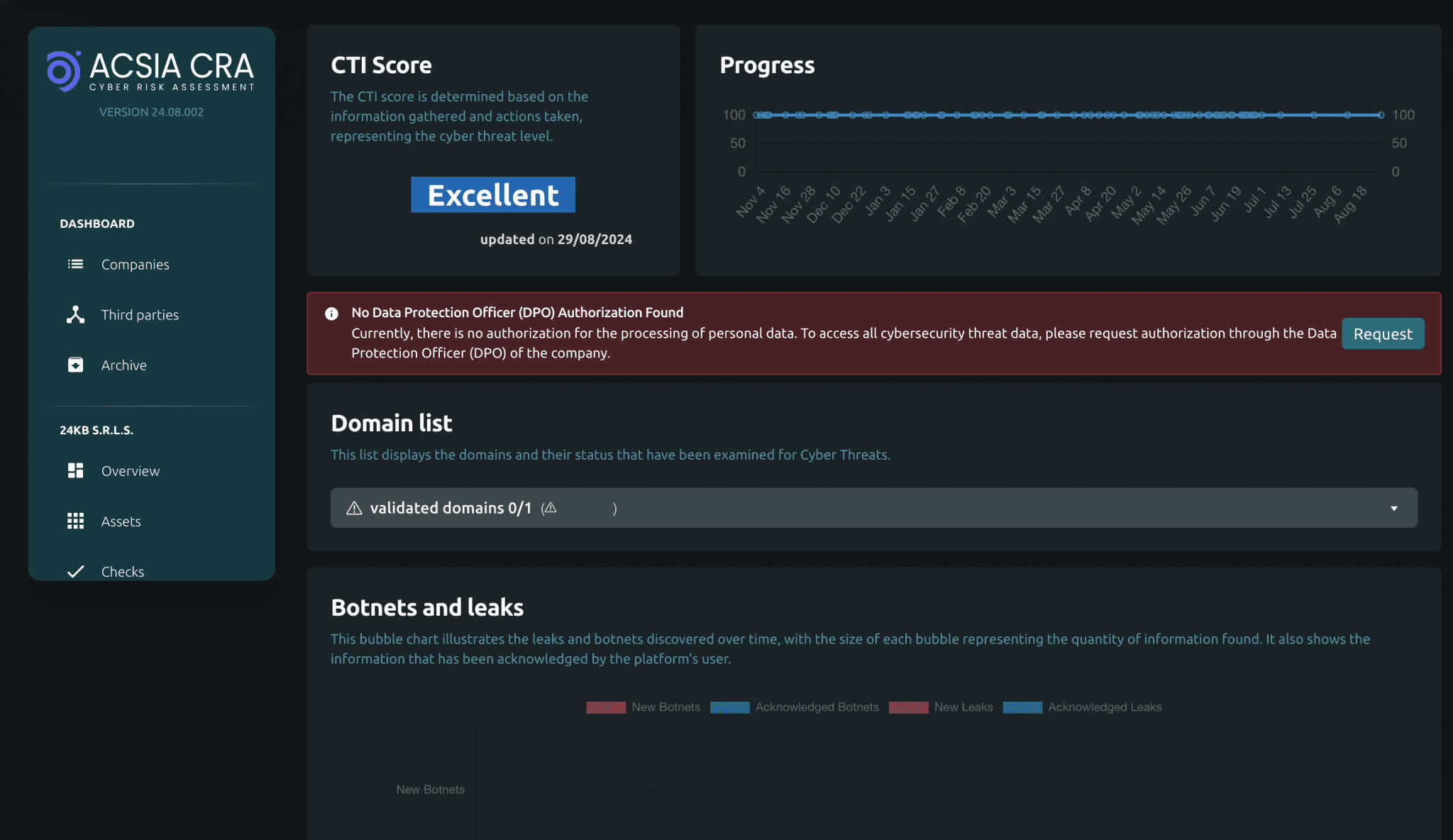
Track Progress Over Time
ACSIA CRA’s risk assessment is summarized in an index that considers six analysis clusters. This analysis produces a score from 0 (unsafe) to 100 (safest).

Know Your Risk Exposure
Your ACSIA CRA’s score represents an overall indicator of the level of risk. Our results are derived from an analysis of the potential exposure of the organization’s assets to cyberattacks.
Identify Vulnerabilities
ACSIA CRA reports provide insight into a range of issues and common vulnerabilities that criminals may spot and exploit to carry out cyber attacks against your business. Empower your team to deal with, and fix vulnerabilities on your organization’s public attack surface, assets and infrastructure.
Document Improvement
Regular scans document how you are improving your ACSIA CRA’s score over time. Demonstrate your company is being proactive for audit, cyber insurance, legislation, GDPR, and certification. Prove that your team is actively working on improving your cyber security.

Are you interested
in learning more about ACSIA CRA? Schedule a virtual meeting with our customer service team to discuss how ACSIA CRA is right for you and your business.